Authentication > Integrate Okta SSO
Integrate Microsoft Entra ID SSO
Connect Microsoft Entra ID (formerly Azure Active Directory) to Tallyfy in about 30 minutes. Your users get automatic login and account creation - no separate passwords needed.
- Microsoft Entra ID administrator access
- Tallyfy Professional or Enterprise plan
- SAML config values from Tallyfy Support
- Create a Microsoft Entra ID enterprise application
- Configure SAML settings in both systems
- Test the connection
You, Tallyfy Support, and Microsoft Entra ID work together through a three-party setup.
Key points:
- Steps 1-10 are one-time setup between you and Tallyfy Support
- Steps 11-15 happen every time someone logs in
- You can’t skip the support ticket (step 1)
-
Sign in to the Azure Portal ↗ with administrator credentials
-
Go to the Microsoft Entra ID service (may still show as Azure Active Directory in some interfaces)
-
Select Enterprise Applications from the Manage section
-
Click +New application
-
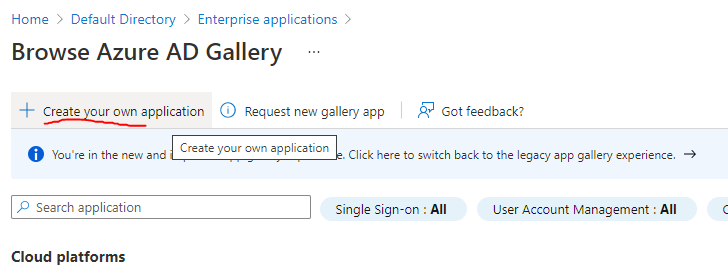
Choose Create your own application
-
Enter “Tallyfy” as the application name
-
Select Integrate any other application you don’t find in the gallery (Non-gallery)
-
Click Create
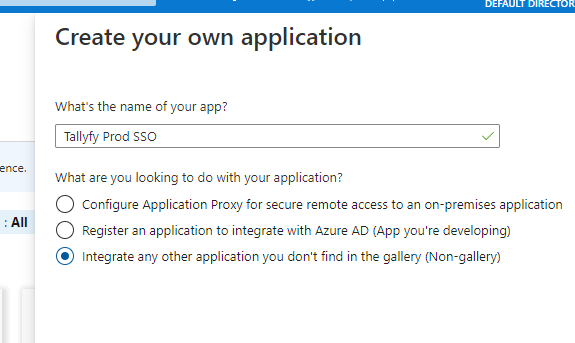
Assign users now or after setup - your choice:
-
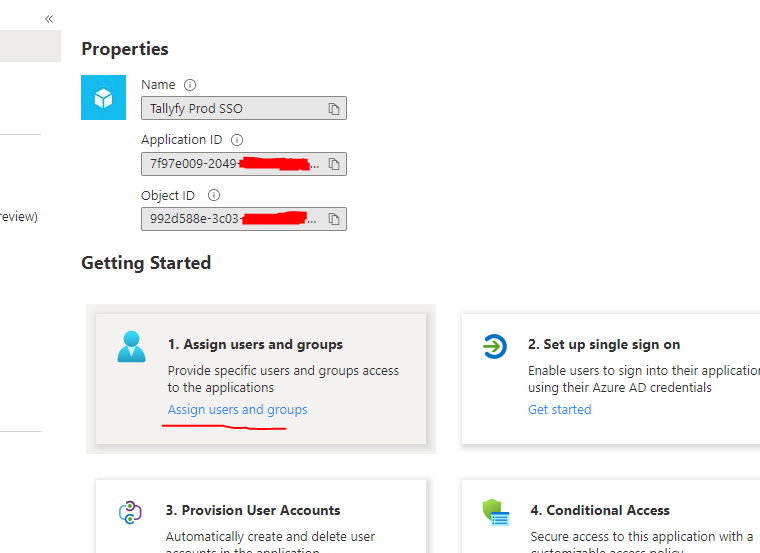
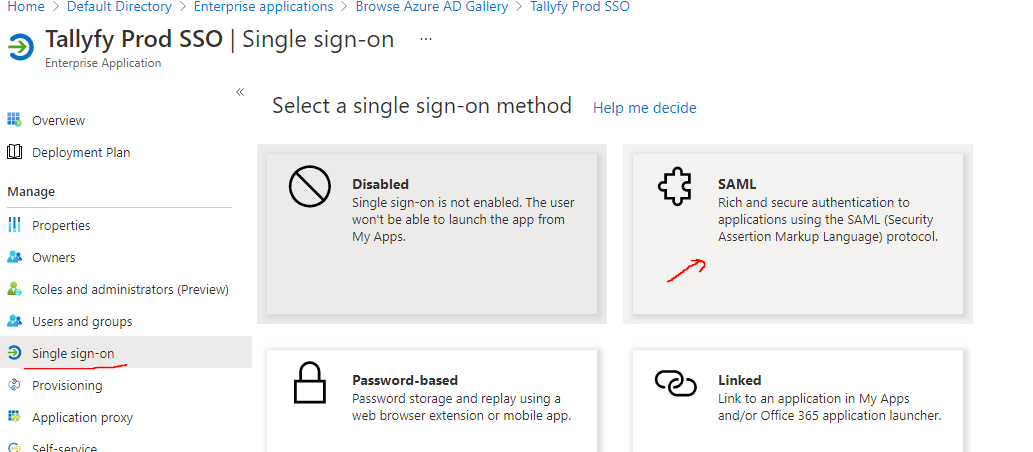
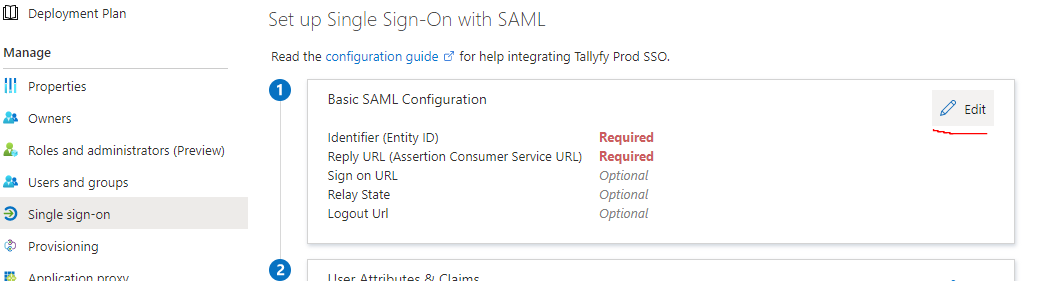
In the application’s sidebar under Manage, select Single sign-on
-
Choose SAML as the sign-on method
-
Click Edit in the Basic SAML Configuration section.
-
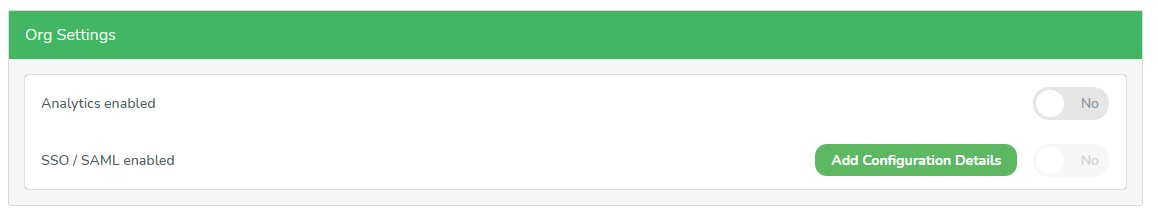
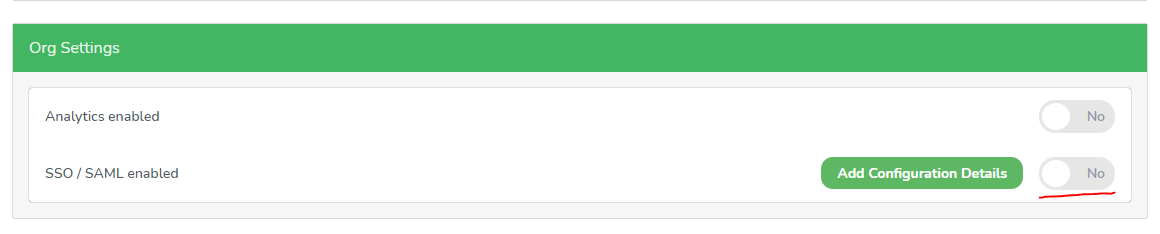
In Tallyfy, go to your organization profile.
-
Open the Org Settings tab.
-
Click Add Configuration Details.
-
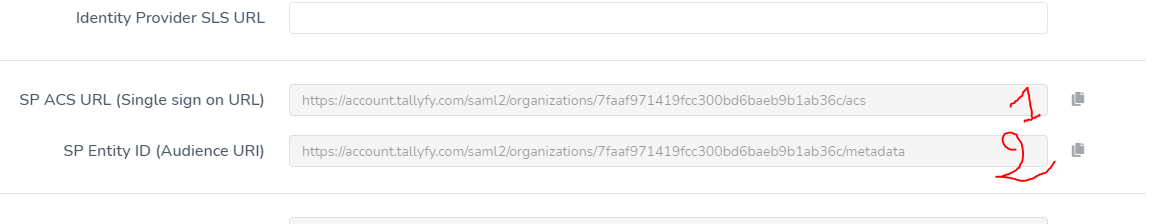
Scroll down to find the default SAML values.
-
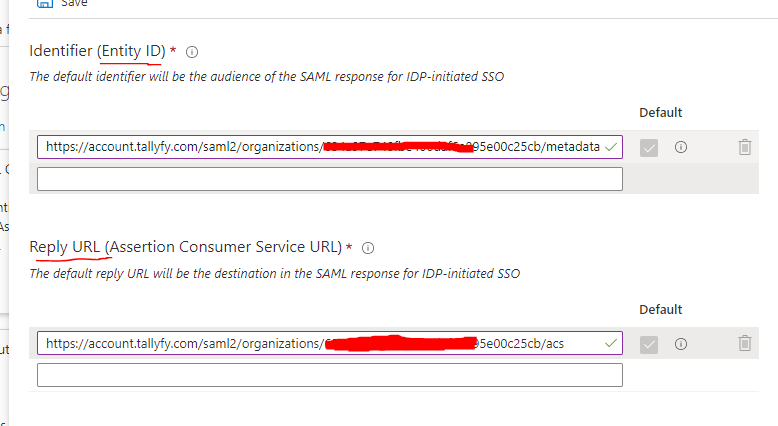
Copy Tallyfy’s SP ACS URL to Microsoft Entra ID’s Reply URL (Assertion Consumer Service URL) field.
-
Copy Tallyfy’s SP Entity ID to Microsoft Entra ID’s Identifier (Entity ID) field.
-
Click Save.
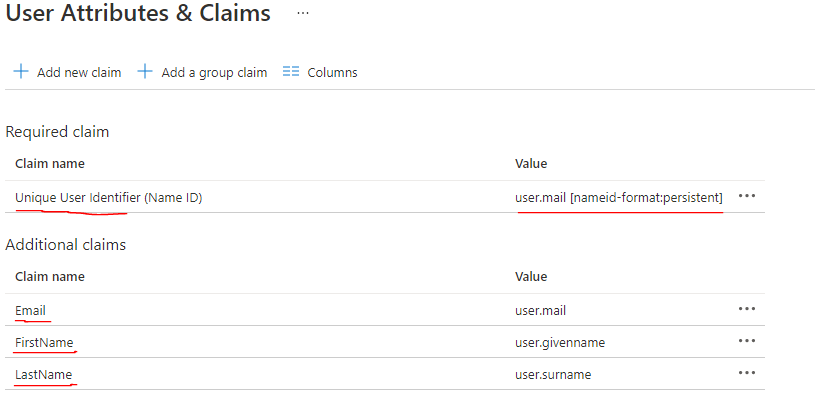
These must be exact - wrong names or capitalization will break user sync.
-
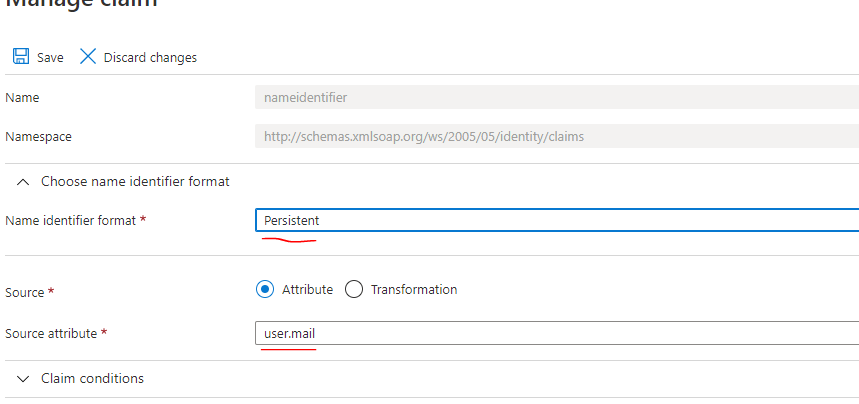
Configure Name Identifier (User ID): Click the Unique User Identifier (Name ID) row.
-
Select Persistent for Name identifier format.
-
Choose user.mail for Source attribute.
-
Click Save.
-
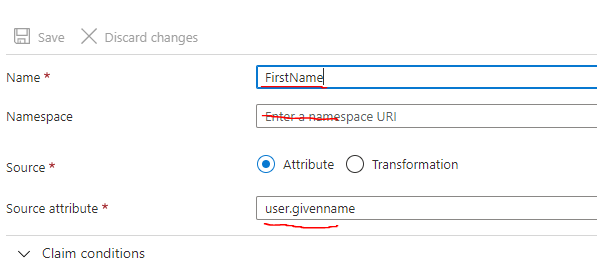
Configure First Name Attribute: Click the attribute row (typically user.givenname).
-
Set Name to:
FirstName(capitalization matters). -
Clear the Namespace field.
-
Set Source attribute to:
user.givenname. -
Click Save.
-
Configure Email attribute: Set Name to
Email, clear Namespace, set Source attribute touser.mail. Click Save. -
Configure Last Name attribute: Set Name to
LastName, clear Namespace, set Source attribute touser.surname. Click Save.
Your final attribute config should look like this:
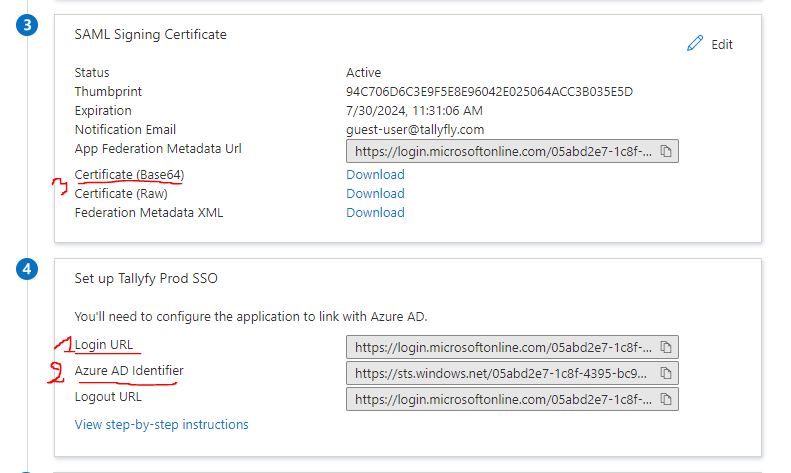
You need three things from Microsoft Entra ID:
-
Go to the Set up section.
-
Copy the Login URL.
-
Copy the Microsoft Entra ID Identifier.
-
Download the Certificate (Base64) from the SAML Signing Certificate section.
-
Send these three items to Tallyfy Support
-
Tallyfy Support configures your SAML settings on their end
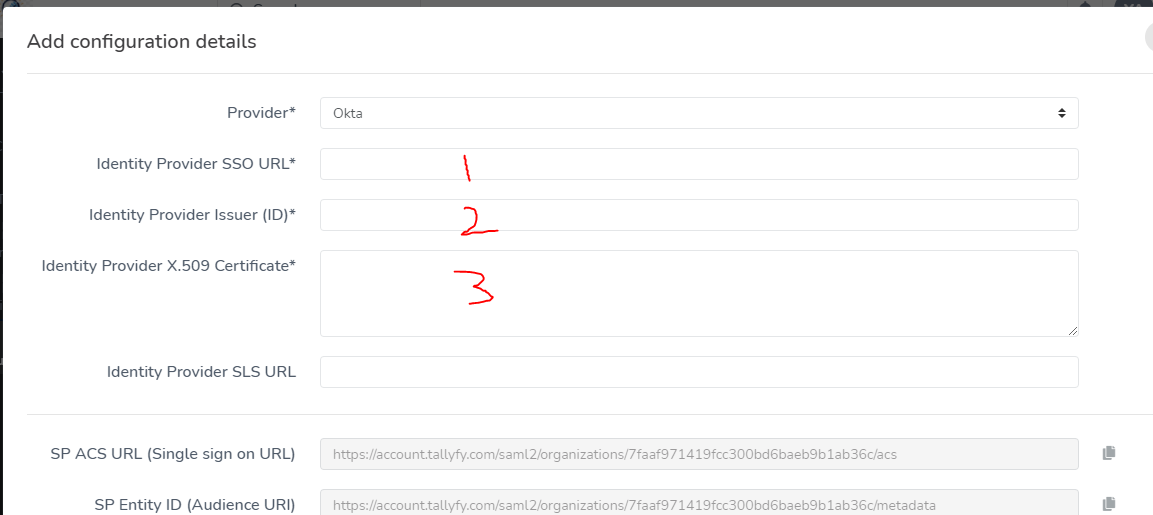
After Tallyfy Support confirms everything’s ready:
-
Turn on the SAML activation toggle
-
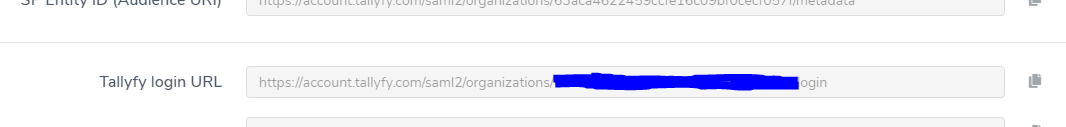
Get your organization’s SSO login URL from the SAML setup modal (Tallyfy Support provides this)
-
Share this URL with your Microsoft Entra ID users
When users visit this URL:
- Existing Tallyfy users log in automatically
- New users get an account created on first login
Users can’t log in? Check these:
- User is assigned to the Microsoft Entra ID application
- Attribute mappings are exact (names and capitalization)
- SAML certificate hasn’t expired
- Users are using the SSO URL (not regular login)
- Still stuck? Contact Tallyfy Support
Integrations > Authentication and SSO
Authentication > Integrate OneLogin SSO
Authentication > Integrate JumpCloud SSO
Was this helpful?
- 2025 Tallyfy, Inc.
- Privacy Policy
- Terms of Use
- Report Issue
- Trademarks